Israeli spyware has been used for surveillance of activists, journalists and political leaders in many nations including India
Israeli spyware has been used for surveillance of activists, journalists and political leaders in many nations including India
By Kiran N. Kumar
Last year, a probe by the Guardian and 16 other media outlets reported that over 30,000 human rights activists, journalists and lawyers across the world may have been targeted by Israeli spyware Pegasus, developed by NSO group.
The report alleged that the malware was deployed widely through a variety of exploits, including several iOS zero-click zero-days. While other mobile manufacturers are caught in inertia, Apple has taken the lead to provide a crucial layer of protection for its new iPhone users.
Read: Apple’s Tim Cook flags concern about green cards going waste (September 28, 2021)
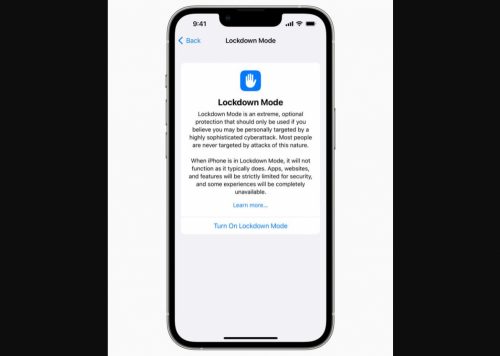
On Wednesday, Apple announced the preview report of its latest anti-Pegasus software called “Lockdown Mode”, to be provided this fall with iOS 16, iPadOS 16, and macOS Ventura.
The new feature is an extreme, optional protection for the very small number of users who face grave, targeted threats to their digital security, said Apple.
“Apple makes the most secure mobile devices on the market. Lockdown Mode is a groundbreaking capability that reflects our unwavering commitment to protecting users from even the rarest, most sophisticated attacks,” said Ivan Krstic, Apple’s head of Security Engineering and Architecture.
Since not all users are victims of such highly targeted cyberattacks, “we will work tirelessly to protect the small number of users who are,” he clarified.
The new security feature is coming after iPhones of high-profile people were targeted by the Pegasus software, which is capable of reading text messages, tracking calls, collecting passwords, location tracking, accessing microphone and camera, and harvesting information from other apps.
The Pegasus spyware has been used for surveillance of activists, journalists and political leaders from several nations, including in India, despite protests by the opposition.
What happens when Lockdown Mode is on?
Apple said that Lockdown Mode offers extreme levels of protection from the most sophisticated digital threats, such as those from NSO Group and other private companies developing state-sponsored mercenary spyware.
Turning on Lockdown Mode in iOS 16, iPadOS 16, and macOS Ventura further hardens device’s defense and strictly limits certain functionalities, sharply reducing the attack surface that potentially could be exploited by highly targeted mercenary spyware, the company explained.
If you need to turn on Lockdown Mode, it’s made simple. Open Settings > Privacy & Security > Lockdown Mode. Choose the option to tap “Turn On Lockdown Mode.”
But once the Lockdown Mode is turned on, most message attachment types other than images are blocked and some features such as link previews are disabled.
Web browsing, of course, gets constrained as complex web technologies, like just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site manually.
Apple services such as incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request.
Wired connections with a computer or accessory are also blocked and configuration profiles cannot be installed, and the device cannot enroll into mobile device management (MDM).
In addition, Apple is making a $10 million grant, in addition to any damages awarded from the lawsuit filed against Pegasus developer NSO Group, to support organizations that investigate, expose, and prevent highly targeted cyberattacks.
Apple has also announced within the Apple Security Bounty program to reward researchers who find Lockdown Mode bypasses to help improve its protections.
“Bounties are doubled for qualifying findings in Lockdown Mode, up to a maximum of $2,000,000 — the highest maximum bounty payout in the industry,” said the company.
Other modes of protection
A joint research report from Amnesty International and Citizen Lab offers a simple but persistent effort to fight the Pegasus infection that relies on zero-click 0-days with no persistence. The report suggested mobile users to regularly reboot.
“If the device is rebooted daily, the attackers will have to re-infect it over and over again. In time, this increases the chances of detection; a crash might happen or artifacts could be logged that give away the stealthy nature of the infection,” said one report.
The format was practically shown in a mobile device targeted through a zero-click exploit (likely ForcedEntry). The device owner rebooted it regularly and did so in the next 24 hours following the attack. The attackers tried to target a few more times but eventually gave up.
Read: Apple expands industry-leading commitment to protect users from highly targeted mercenary spyware (July 6, 2022)
Other tips to avoid Pegasus include — not to click on links received in text messages, browse the internet with an alternate browser such as Firefox Focus instead of the default Chrome, use a VPN that masks your traffic, be cautious while browsing HTTP sites for DNS hijack and install a security suite to scan malware and warn if the device is rooted.
As Lockdown Mode will be put to litmus test in the coming few months, the iPhone maker is readying for the next big battle.